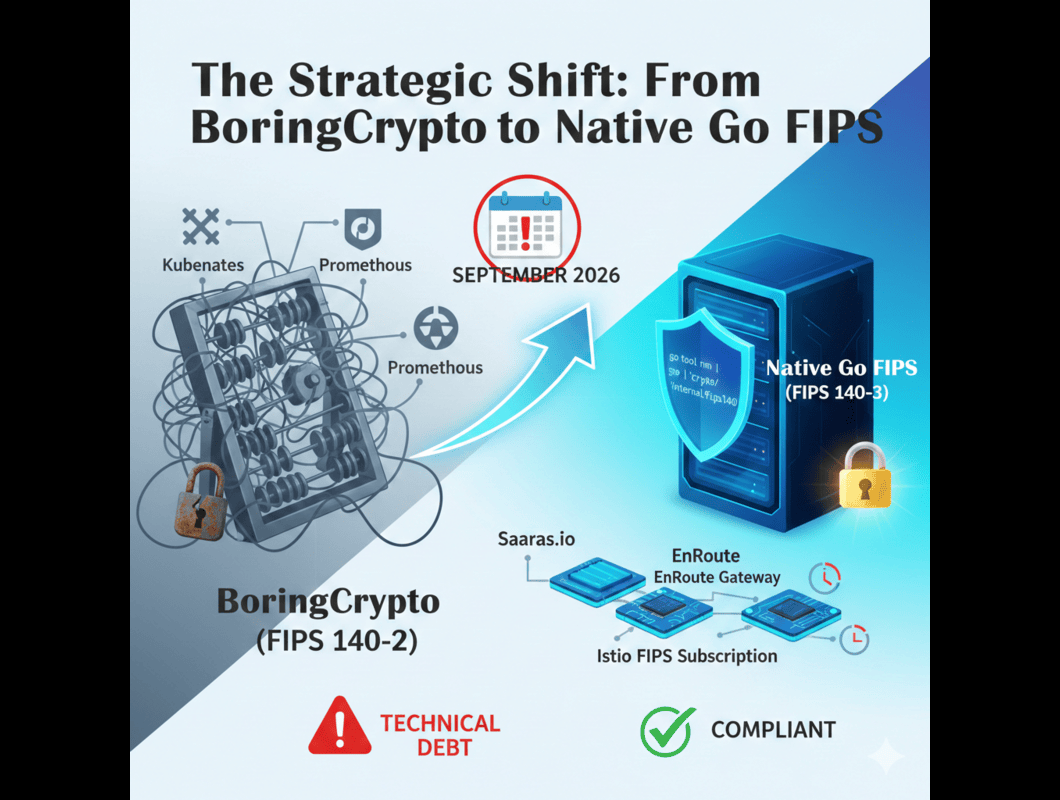
The Strategic Shift: From BoringCrypto to Native Go FIPS
For years, the industry standard for securing Go applications (like Kubernetes, Istio, and Prometheus) was BoringCrypto. This was a workaround that forced Go to call out to a C-based, FIPS-validated library created by Google. It worked, but it was slow, complex, and hard to maintain.
With Go 1.24, everything has changed. The Go language now includes a native FIPS 140-3 module.
- Old Way (Legacy): Relied on "BoringCrypto" wrappers (CGO). Complex build chains, performance penalties, and stuck on the expiring FIPS 140-2 standard.
- New Way (Modern): Native Go FIPS. Written in pure Go/Assembly. Faster, easier to compile, and aligned with the new FIPS 140-3 mandates.
Strategic Takeaway: You must audit your software supply chain. If your vendors are still shipping "BoringCrypto" builds after September 2026, they are handing you technical debt that may fail a 3PAO audit.
Technical Audit: How to "Verify FIPS"
As a leader, you need to trust but verify. You can check if your binaries are compliant using simple command-line tools. Ask your DevOps leads to run these checks on your critical images.
1. Identifying Legacy BoringCrypto (The Old Standard) Run this command on your current binaries (e.g., Istio sidecars or API gateways)
Bash
go tool nm <path-to-binary> | grep _Cfunc__goboringcrypt
- Result: If you see symbols like _Cfunc__goboringcrypto_SHA256, you are using the legacy module. This is valid today, but you must plan your migration to FIPS 140-3.
2. Identifying Native Go FIPS (The Future) For modern binaries built with Go 1.24+:
Bash
go tool nm <path-to-binary> | grep "crypto/internal/fips140"
- Result: Presence of crypto/internal/fips140 confirms you are using the modern, future-proof stack.
Understanding FIPS BoringSSL v1.7
This section addresses the specific "FIPS BoringSSL v1.7" module often found in current compliance reports.
If you audit your current Android-based endpoints, Google Cloud appliances, or legacy container images, you will frequently see the cryptographic module identified as "FIPS BoringSSL v1.7"(often referencing NIST Certificate #4735 or similar). This version represents a specific, widely deployed build of the BoringCrypto core that powers millions of devices and servers.
While "v1.7" is a gold standard for FIPS 140-2 compliance today, it represents a strategic risk for tomorrow. Because it is validated under the 140-2 standard, it falls squarely into the "Historical List" transition. Come September 2026, systems relying strictly on this version without a roadmap to a FIPS 140-3 update (often referred to as BoringCrypto/BoringSSL FIPS 140-3) will be non-compliant for new federal procurements. When reviewing vendor roadmaps, do not accept "We use BoringSSL v1.7" as a long-term answer. You must ask: "When are you transitioning this module to a NIST-validated FIPS 140-3 certificate?"
The "Easy Button" for Compliance: Saaras.io
Rebuilding your entire stack to handle these cryptographic changes is expensive and risky and provides a turnkey alternative that allows you to "inherit" compliance rather than building it from scratch.
1. The FIPS Stack
Saaras provides a complete suite that includes pre-hardened, FIPS-validated versions of Istio and Envoy. We track the NIST validations so you don't have to.
- Benefit: Reduces FedRAMP ATO timelines from 18 months to ~6 months.
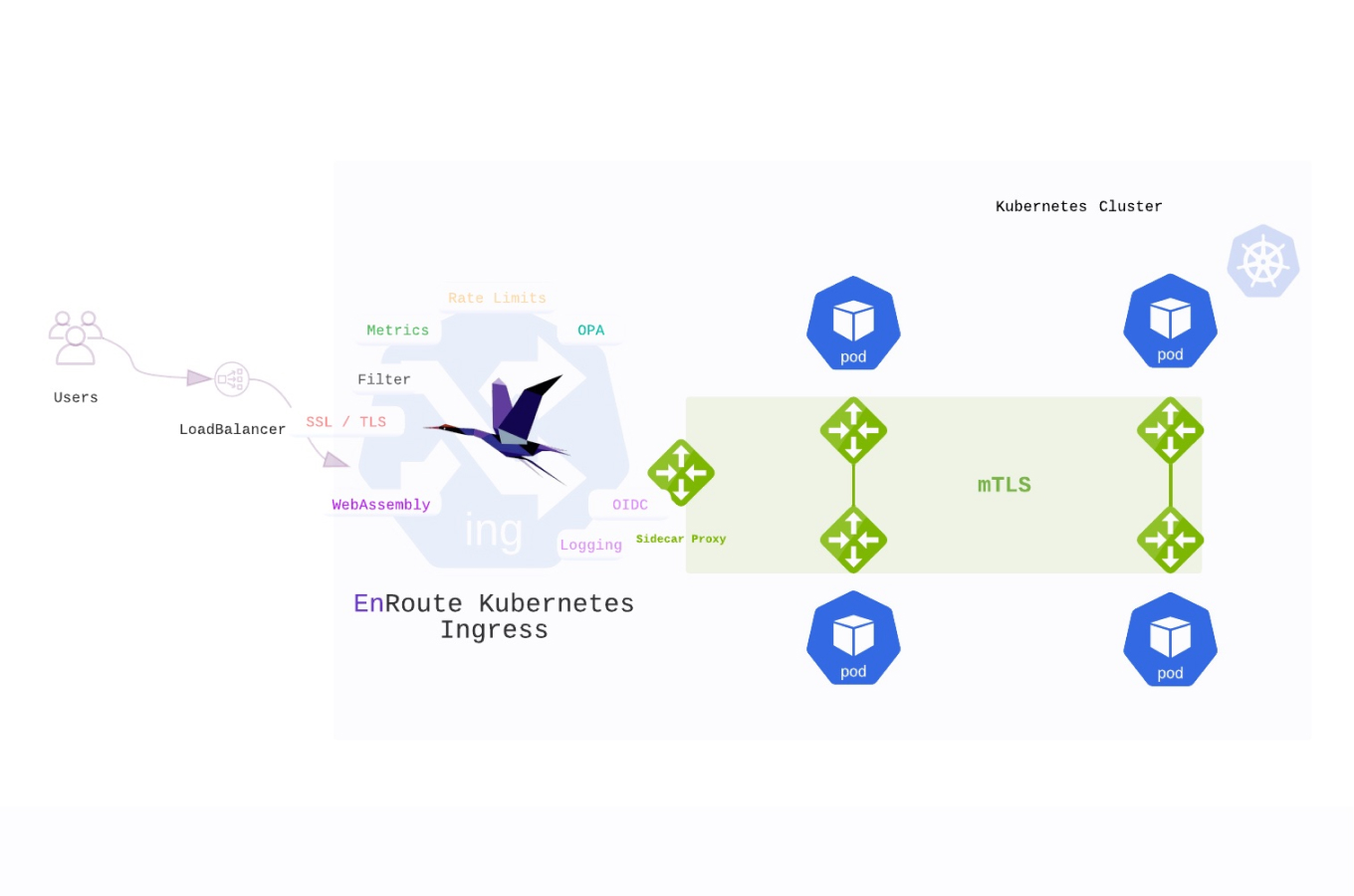
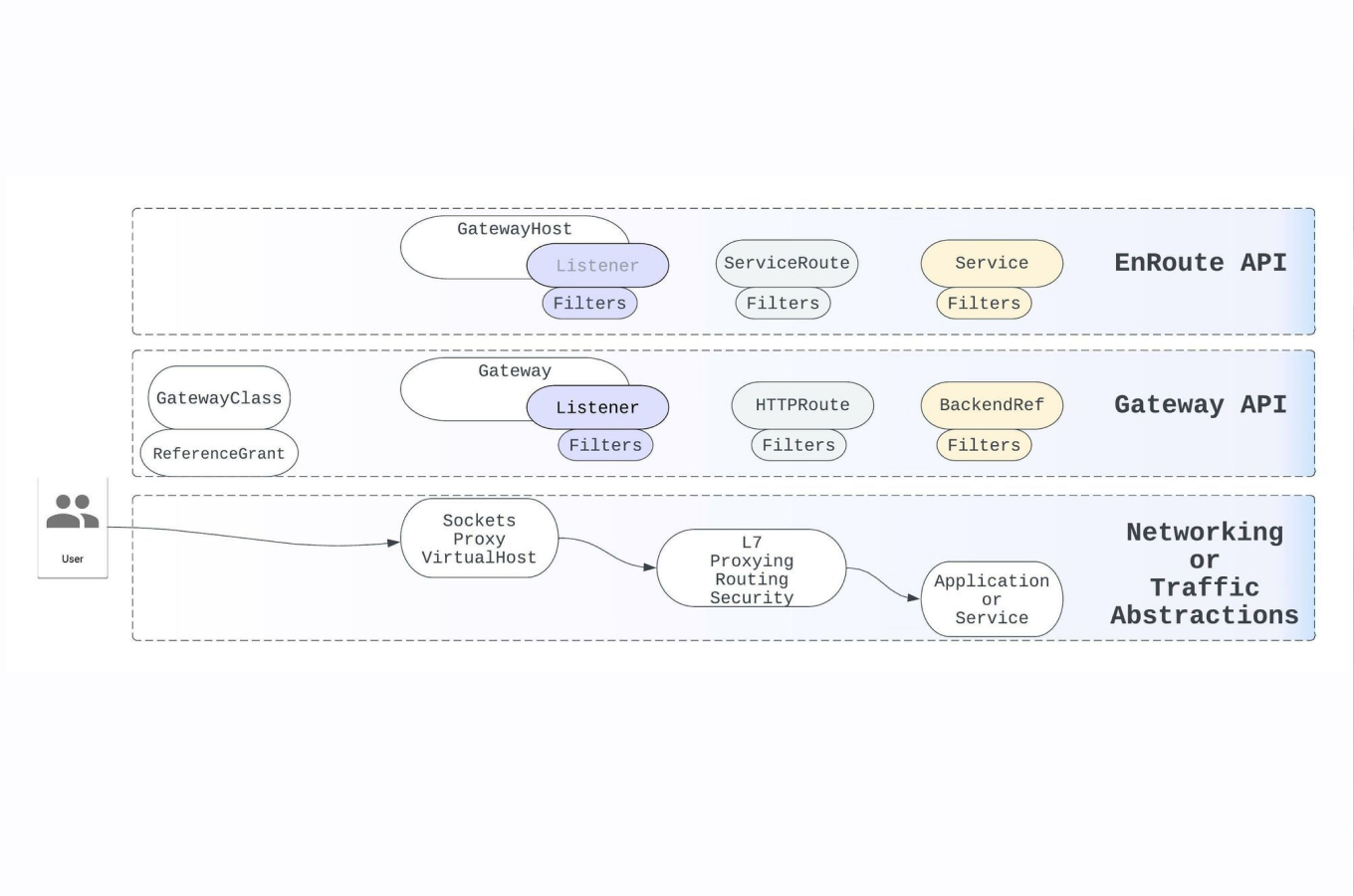
2. EnRoute Gateway
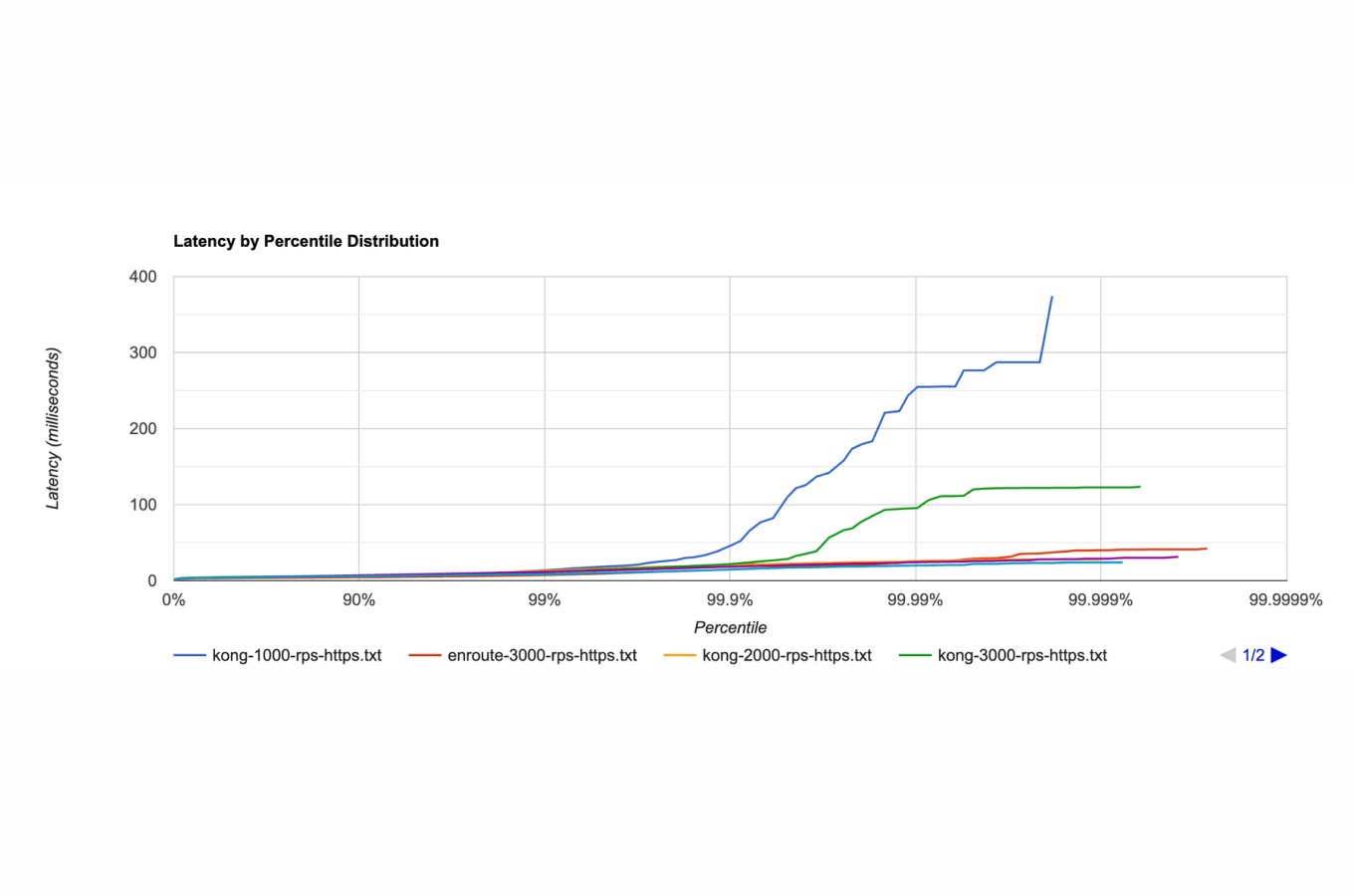
Secure your cluster perimeter with the enroute gateway. It replaces standard Ingress controllers with a FIPS-ready Envoy build, ensuring traffic entering your cluster is encrypted using approved ciphers immediately.
3. Istio FIPS Subscription
For East-West traffic (service-to-service), Istio FIPS offers a drop-in replacement for open-source Istio.
- Zero Lock-in: 100% upstream compatible.
- SLA-Backed: Periodic CVE patching ensures you meet the strict 30-day remediation windows required by federal auditors.
Conclusion
The transition to FIPS 140-3 and Go 1.24 is the biggest shift in federal cryptography in a decade. With the September 2026 deadline less than a year away, the time to audit your "Verify FIPS" procedures is now.
Don't let compliance slow you down. Explore the blogs for more technical deep dives, or contact us to secure your infrastructure today.
The primary difference lies in the architecture and compliance standards. BoringCrypto is a legacy workaround (FIPS 140-2) that uses CGO to link Go applications to a C-based library. Native Go FIPS, introduced in Go 1.24, is written in pure Go and Assembly. It supports the newer FIPS 140-3 standard, offers better performance, and simplifies the build process by removing C dependencies.
The fastest way to achieve a FedRAMP Authority to Operate (ATO) is to "inherit" compliance from validated infrastructure. By using a FIPS-hardened stack—such as the EnRoute Gateway and Istio FIPS Subscription from Saaras-you can reduce the compliance timeline from 18 months to approximately 6 months. This approach offloads the burden of NIST certificate tracking and CVE patching to a dedicated provider.
Yes, Go 1.24 is a landmark release that includes a native FIPS 140-3 module. This allows developers to build compliant applications without the performance penalties of CGO, making it the recommended path for Kubernetes, Prometheus, and other cloud-native tools transitioning away from the BoringCrypto era.